Okta Japan Publishes 'Businesses at Work 2026' Report Revealing 11x Surge in AI Agent-Driven Access Requests
The AMW Read
The report meaningfully updates the baseline on AI agent-driven access growth and NHI security gap, with cross-segment compute implication, but does not resolve an open debate.
Okta Japan Publishes 'Businesses at Work 2026' Report Revealing 11x Surge in AI Agent-Driven Access Requests
Okta Japan released its annual 'Businesses at Work 2026' report, analyzing data from the Okta Integration Network (OIN) covering November 2024 to October 2025. The report highlights a dramatic increase in AI agent-driven access requests, which surged 1140% over two years, with an annual increase of 158%. The number of service accounts managed per organization grew 650% year-over-year, driven by the proliferation of non-human identities (NHIs) from AI agents and automated processes.
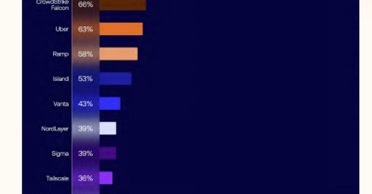
The rapid adoption of AI agents is creating a fundamental identity security challenge. As NHIs multiply — with media/telecom averaging 78 service accounts per organization and tech firms 28 — most organizations still manage fewer than 5 service accounts, leaving the majority ungoverned. The report emphasizes that gaining visibility and control over NHIs is a prerequisite for safe AI agent deployment. Moreover, the shift toward stronger authentication is accelerating: phishing-resistant MFA adoption rose from 41% two years ago to 58%, and Okta FastPass passwordless authentication grew 81% year-over-year.
The AI identity security gap highlighted by this report exemplifies a cross-substrate tension: the compute-driven surge in AI agents (cross.§A) is colliding with enterprise security posture. The non-human identity blind spot is a classic 'context-engineering moat' failure — the speed of AI deployment outpaces governance. Enterprises that solve this NHI management challenge will gain a structural advantage, while those that ignore it risk catastrophic privilege escalation. This also updates the open debate around agentic security, validating the thesis that identity infrastructure must evolve to handle machine-to-machine authentication at scale.